Recently I have had to fix everything.
Read more →
I went to the local food store. Saw a truck with a bunch of antennas. Struck up a conversation.
Not a ham!
Maybe I can help.
Read more →
Or, Open Source as a marketing buzzword
Read more →
A response to @abraxas3d@defcon.social.
Read more →
What counts as Amateur radio? Is meshtastic on ISM to be considered ham radio?
Read more →
ARRL’s Logbook of the World has a full public key infrastructure.
This can be handy if you need to bootstrap some kind of auth or PKI from a large group of existing users.
Read more →
When I was looking for ham clubs, age difference wasn’t the underlying
problem. It was the attitudes. Any number of them.
Read more →
Docker won’t run cross-platform containers any more. What gives?
Read more →
 Read more →
Read more →
Continuing the paragliding, skydiving, and being recently unemployed
trend of worrying my parents and friends, I bought a motorcycle.
Read more →
I got laid off! Along with a huge chunk of the company.
Read more →
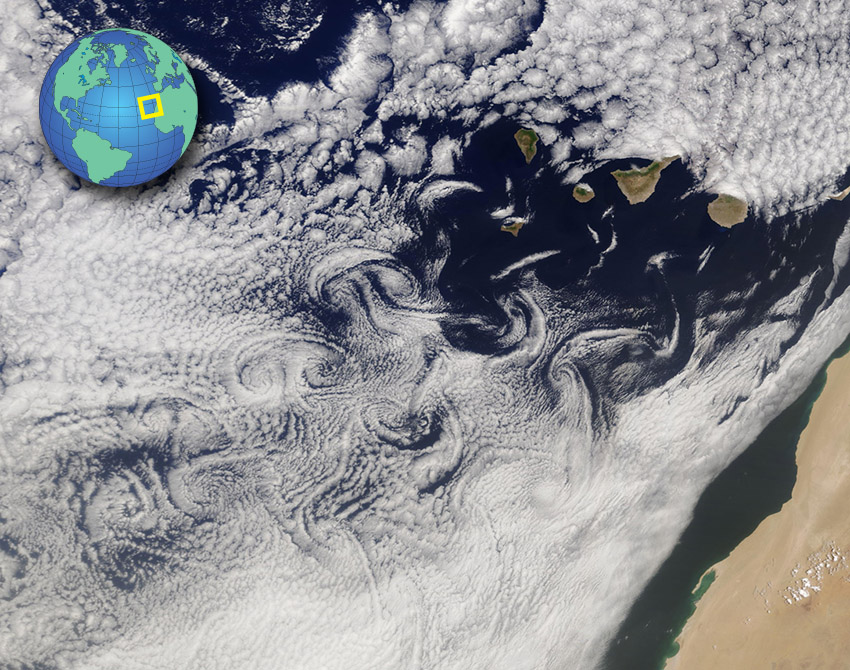
Really cool example of turbulent air caused by some mountains. Ran across
this and I’m keeping it here as a cool way of showing just how big
turbulence can be.
Read more →
(Paragliding)
This is a must-watch video on throwing the reserve where we see the
generally poor safety culture in paragliding get a massive kick in
the butt.
Read more →
M17 is an open source land
mobile radio digital voice and data protocol, and the M17
Project is a worldwide community implementing
that protocol.
M17 is fully open including the voice codec. Competitor protocols have
proprietary codecs, which limits their hackability and your freedoms.
This is M17. Experiment, innovate, learn, build and fix at your own will.
Benefit from others doing the same thing. Repeat!
Read more →
Hi everyone! I made and maintain https://dmr.tools/ and would like your
feedback on it, especially if you’ve been using it over the years, and your stars on the github source
Read more →
Chip posted this the other day titled “Open Letter to MMDVM Board/Hotspot Vendors”.
I don’t have much to add. I’ve been bitten by this too. Many hotspot
vendors are skimping on quality or other various aspects, or otherwise
sell you something that is artificially limited.
I figured I’d link his post for what little extra attention it might gain his message,
and mention a couple sellers that are good while I’m at it.
Read more →
In land mobile radio, it can be handy to have a legible shorthand
for describing a channel. Over time we’ve seen one evolve, that I’ve
formalized a bit to implement in dmr.tools.
Read more →
Yaesu’s FTM-300 mobile VHF/UHF radio has a bug related to decoding digital data from the data port in the back.
Read more →
Daniel Stenberg’s guide and writing are excellent.
I discovered the hard way that the cable for Hytera PD362s from
BlueMax49ers was not correctly made on multiple levels. (Written early June 2023)
Read more →
This applies exactly as well to the MD-UV390, RT3S, the GPS variants, etc, as they are all the same radio. Is this advice for you, or reminders for me? Hard to tell sometimes.
Recommended tools Hot air, for desoldering, or good quality desoldering tweezers. Stereo microscope (!! very important !!) finest tip for your iron you can find no caffeine, good nights rest, an hour after eating (otherwise your hands will shake a lot more) antenna washer removal tool Taking it apart Buy that $15 antenna washer removal tool.
Read more →
The FCS-152 is a visual clone of
the PRC-152 that offers FM analog VHF/UHF voice communications.
Read more →
If you play the flight simulator DCS World and happen to have a bass
shaker or buttkicker handy, and are comfortable with Python, you’ll
want this.
Read more →
This is meant to be a series of short and sweet guide to a few ways to run M17 over RF today.
This one focuses on transmitting and receiving M17 with m17-cxx-demod and GnuRadio.
This’ll require a little more Linux familiarity than the OpenWebRX guide, but it’s not too bad.
I’d say the hardest part is making sure you have the right dependencies
installed - on some linux systems it can be a real bear. If you run into
any troubles, make sure to ask for help
and we’ll try to sort it out and get it documented.
Read more →
What’s new?
Read more →
This is meant to be a series of short and sweet guide to a few ways to run M17 over RF today. This one focuses on receiving M17 with OpenWebRX.
Read more →
What’s new?
M17:
Building a presentation- Going to do the hardware mods for MD-380 and MD-UV380
- Should get grant money soon.
CW/Morse:
- Emailed the VBand folks about what I built.
OpenRTX:
- Satellite tracking/pass prediction
I’ve just pushed the first version of DMR.Tools with a backend server. The highlight for this release is the easy firmware upgrade to OpenRTX releases, and the easy flashing of OEM firmware.
There’s a LOT more coming, (codeplug editing!) but it’s not fully ready so it’s disabled right now.
I got firmware updates through WebUSB working for 1st and 2nd gen TYT radios last night. Previously it onl;y supported 1st gen (single banders).
Read more →
2020 has been a hard year. With family medical issues, a dying (and now
passed) dog, the end of 2020 was particularly rough.
There’s one bright point - I soft launched DMR.Tools, specifically to help my first user.
Read more →
Sorry, not up to writing a blog post about this. It works great though.
tarxvf: I made a thing (still needs polishing but PoC works great!) that takes snapshots of a file every time it’s saved. This means you record your screen while editing the codeplug and verbally describe what you’re doing. Make one change per saved file. Extract the audio, use whisper-timestamped to get a transcript. If you say ‘mark’ every time you save a file, you know where things will line up.
Read more →
Some new updates for ProgramRadios/DMRTools involving encryption keys.
Read more →
Open Research Institute (ORI) has sponsored us (M17)!
Check us out on their projects page, and keep reading to see why this is good for M17.
Read more →
Obligatory new website post. Redid the website to be cleaner and simpler using Hugo this time.
Vehicle Tracking: EZPass, ALPR, Cashless Tolling, TPMS EZPass Beyond Tolls DEF CON 21 (2013) Security researcher “Puking Monkey” built portable EZPass detector, drove around NYC. Detected EZPass readers mounted on infrastructure at locations with no toll plazas — on highways, at intersections, near Brooklyn Battery Tunnel approach.
NYC DOT confirmed using EZPass readers for traffic flow monitoring since at least 2011, measuring travel times between points. Not secret but not widely publicized.
Read more →
TSA Malfeasance and Travel Privacy Regulatory Authority Papers Please / Identity Project (papersplease.org) argues TSA conducts screening without valid regulations. TSA relies on Security Directives and Emergency Amendments — non-public orders — rather than properly promulgated regulations under the APA (notice-and-comment rulemaking).
EPIC v. DHS (D.C. Circuit, 2011): Court ruled TSA violated APA by deploying body scanners without notice-and-comment period. Ordered TSA to conduct one. TSA delayed compliance for years.
Read more →
Third-Party Doctrine / Fourth Amendment The Doctrine Information voluntarily given to a third party (bank, phone company, ISP, ad network) carries “no reasonable expectation of privacy.” Government can obtain it without a warrant.
Key Cases Smith v. Maryland (1979) Police used pen register to record phone numbers dialed by robbery suspect. No warrant. SCOTUS: no Fourth Amendment violation. Caller “voluntarily conveyed” numbers to phone company and assumed risk of disclosure.
Read more →
Target Pregnancy Prediction Source Charles Duhigg, “How Companies Learn Your Secrets,” New York Times Magazine, February 16, 2012.
How It Worked Target statistician Andrew Pole tasked with identifying pregnant customers from purchase data. Target assigned each customer a “Guest ID” linked to credit card, loyalty card (TargetRed), name, email, and purchase history.
Pole identified ~25 products whose purchase patterns correlated with pregnancy stages: unscented lotion, supplements (calcium, magnesium, zinc), cotton balls, hand sanitizers, washcloths.
Read more →
Structural Points: Connective Tissue for the Essay The Consent Fiction Carnegie Mellon study (Aleecia McDonald and Lorrie Faith Cranor, 2008, “The Cost of Reading Privacy Policies”): average person would need ~76 work days per year to read all privacy policies they encounter. Consent is structurally meaningless at scale. Every data collection practice documented in these research files occurs under terms nobody reads.
Public Records as the Base Layer Most data collection builds on top of freely available public records:
Read more →
Strava Heat Map, Fitness Trackers, and Health Data Privacy Strava Heat Map (January 2018) Strava published global heat map (November 2017) showing 3 trillion GPS data points from users. Went viral January 2018 when Nathan Ruser (20-year-old Australian National University student) posted analysis showing the map revealed:
Locations and layouts of military bases in Afghanistan, Syria, Djibouti, Niger Patrol routes and exercise patterns at forward operating bases Locations believed to include CIA black sites and classified facilities Personnel movements visible because soldiers/agents used Strava while exercising.
Read more →
Soviet Union: Internal Passports and Census Data Internal Passport System (December 1932) Required all urban citizens to carry documents listing name, DOB, nationality (ethnicity), and registered address (propiska). Nationality — the “fifth line” (pyataya grafa) — assigned by state based on parentage, not self-selected. Created permanent ethnic classification of entire population.
Soviet Censuses 1937 Census (Suppressed) Conducted January 1937. Revealed population of ~162 million — roughly 15-17 million fewer than projections.
Read more →
Social Credit Parallels and FinCEN / Bank Secrecy Act China’s Social Credit System Launched formally 2014 (State Council plan). Aggregates government and commercial data to rate individuals and businesses. Consequences for blacklisted individuals:
Airline ticket purchases blocked 23 million times (as of 2018, National Public Credit Information Center) High-speed rail blocked 6 million times Throttled internet speeds Exclusion from private schools Public naming on court-maintained defaulter list Western Analogs FICO Scores Created by Fair Isaac Corporation (1989).
Read more →
Smart TV Surveillance, Voice Assistants, and Library vs. Commercial Reading Data Smart TV Automatic Content Recognition (ACR) How ACR Works Samples visual content displayed on screen at intervals (typically every few seconds), generates compact fingerprint/hash of pixel data, compares against reference database. Works across ALL inputs — streaming apps, HDMI, antenna, DVD, game console, anything rendered on the display.
Major ACR providers: Samba TV, Inscape, Gracenote.
Roku ACR technology captures visual fingerprints of on-screen content at regular intervals — including from HDMI inputs (cable boxes, game consoles, Blu-ray players, DVDs).
Read more →
ShotSpotter, Border Device Searches, and Fusion Centers ShotSpotter / SoundThinking Deployment ~150+ US cities at peak. Rebranded from ShotSpotter to SoundThinking (2023).
How It Works Acoustic sensors (mounted on buildings/poles) detect impulsive sounds consistent with gunfire. Multiple sensors triangulate location via time-of-arrival differences. Alerts sent to review center where analysts classify sound before forwarding to police (30-60 seconds).
False Positive Rate MacArthur Justice Center (2021, Chicago data): 89% of alerts led to police finding no evidence of gunfire or gun crime Chicago OIG (August 2021): 86% of dispatches resulted in no incident report of gun-related offense SoundThinking disputes: “no evidence found” does not equal “false positive” Chicago Deployed ~2017-2018, expanded under Mayor Lightfoot.
Read more →
Commercial Satellite Surveillance Capabilities (2025) Optical/Visual Imaging Maxar (WorldView Legion) First satellites launched June 2023. Native resolution: ~30 cm. Effective ~15 cm class product via processing. Revisit: up to 15 times/day for mid-latitude targets. Tasking available to commercial and government customers.
Planet Labs ~200+ Dove satellites (“SuperDoves”): entire Earth’s landmass daily at 3-5 m resolution. SkySat constellation (21 satellites): ~50 cm resolution, sub-daily revisit, video capture (up to 90-second clips). Pelican constellation (launches began 2024): targets 30 cm resolution.
Read more →
Russiagate, Steele Dossier, and Intelligence Community Surveillance The Steele Dossier Series of memos compiled 2016 by Christopher Steele, former MI6 officer, through his firm Orbis Business Intelligence. Steele hired by Fusion GPS, contracted by law firm Perkins Coie on behalf of Clinton campaign and DNC (FEC conciliation agreement, March 2022).
Alleged Russia had compromising material on Trump and ongoing conspiracy between Trump campaign and Kremlin. Most salacious claims (including “pee tape”) never corroborated.
Read more →
Real-Time Bidding (RTB) / Programmatic Advertising Bid Request Contents (OpenRTB 2.5/2.6 spec) Device ID (IDFA on iOS, GAID on Android) IP address GPS-precise latitude/longitude User-Agent string Exact page URL being visited Page content categories (IAB taxonomy) User segment/interest data Age, gender Carrier info Spec: https://iabtechlab.com/standards/openrtb/
Volume Google Authorized Buyers: 747 billion bid requests in the US in 2019 Google global: ~4.4 trillion bid requests in 2019 Total global RTB across all exchanges: hundreds of billions per day Data Distribution Each bid request broadcast simultaneously to dozens to hundreds of entities (DSPs, SSPs, ad exchanges, data management platforms).
Read more →
Mesh Routers, ISP Data Collection, and DNS Surveillance Proprietary Mesh Routers What Any Router Operator Sees All device MAC addresses, all DNS queries (unless DoH/DoT), traffic volume per device, connection timestamps, destination IP addresses, which services contacted.
Google Nest WiFi / Google WiFi Privacy policy: collects device MAC addresses, network performance data, usage statistics. Cloud services process DNS queries by default. Google Home app shows device connection/disconnection times (presence detection). Policy permits aggregation across Google services.
Read more →
Ring / Neighbors App as Distributed Surveillance Network Scale Amazon acquired Ring in 2018 for ~$1 billion. By 2023: estimated 20+ million devices in US. Neighbors app (launched 2018): 10+ million Android downloads. In some neighborhoods, camera density exceeds one per 5-10 homes.
Police Partnerships Before January 2023 2,000+ law enforcement agency partnerships by 2022. Police had access to Request for Assistance (RFA) portal: could ask Ring users within defined geographic area and time window to voluntarily share footage WITHOUT warrant.
Read more →
Right to Travel: Supreme Court Cases Key Cases Crandall v. Nevada, 73 U.S. (6 Wall.) 35 (1867) Struck down state tax on passengers leaving by commercial carrier. Right to travel between states is fundamental right implicit in national citizenship.
Kent v. Dulles, 357 U.S. 116 (1958) Right to travel is “a part of the ’liberty’ of which the citizen cannot be deprived without due process of law under the Fifth Amendment.
Read more →
Search History & Reverse Warrants Keyword Warrants Police ask Google for identifying information on ALL users who searched specific keywords during a time window. Reverses traditional warrant model: instead of “show me what this suspect searched,” it’s “show me everyone who searched for X.”
People v. Seymour (Colorado Supreme Court, 2023) Police used keyword warrant to ask Google for anyone who searched variations of a home’s street address in two weeks before arson that killed five people.
Read more →
Payment Processors PayPal Blanket prohibition on firearms transactions.
Stripe Shut down payment processing for Gab. Blocked donations to Trump’s campaign.
Firearms Merchant Category Code (MCC) 2022: ISO adopted new four-digit MCC for gun/ammunition shops, at urging of Amalgamated Bank (New York) working with gun control groups Previously gun shops lumped with general sporting goods stores Visa, Mastercard, American Express initially agreed to implement, then paused after backlash from Second Amendment advocates California passed law requiring firearms retailers to adopt the code by May 2025 Multiple red states passed laws prohibiting the code The MCC shows that a transaction occurred at a gun store and the total amount; does not show individual items purchased Sources https://www.
Read more →
Patio11 (Bits About Money) — Debanking Summary Source: https://www.bitsaboutmoney.com/archive/debanking-and-debunking/
Patrick McKenzie’s article — primarily about crypto debanking, broadly applicable:
SAR regime: ~4M SARs/year, banks cannot tell customers, second SAR triggers closure, no appeals. Secrecy codified at 12 CFR 21.11(k).
“Sontaku” compliance culture: Japanese concept — banks anticipate regulator preferences and implement without being asked.
Enhanced Due Diligence (EDD) as gate: Banks without EDD for high-risk categories refuse service rather than develop controls.
Read more →
Palantir in Local Policing LAPD Contract began 2009, initially funded by In-Q-Tel (CIA venture arm), later by city. Integrated crime reports, field interview cards, ALPR data, other records into unified platform.
Operation LASER (2011-2019) Los Angeles Strategic Extraction and Restoration. Predictive policing using Palantir software. Generated “Chronic Offender Bulletins” scoring individuals by predicted risk of violent crime involvement. Officers directed to make contact with people on lists.
Ended April 2019 after criticism from Stop LAPD Spying Coalition and internal audit finding inconsistent/unreliable point assignments, racial bias concerns, lack of oversight.
Read more →
NSA Mass Surveillance: Snowden Revelations PRISM (US-984XN) Launched 2007 under Section 702 FISA Amendments Act. NSA collected data directly from servers of nine tech companies: Microsoft (2007), Yahoo (2008), Google (2009), Facebook (2009), PalTalk (2009), YouTube (2010), Skype (2011), AOL (2011), Apple (2012). Data: emails, chat logs, stored files, voice/video calls, photos, social networking details. Disclosed: Guardian and Washington Post, June 6, 2013.
XKeyscore NSA search system. Training materials: covers “nearly everything a typical user does on the internet.
Read more →
NFA History and Registry National Firearms Act (1934) Enacted June 26, 1934. Response to Prohibition-era gang violence. Regulates six categories: machine guns, short-barreled rifles (SBRs), short-barreled shotguns (SBSs), suppressors/silencers, destructive devices, Any Other Weapons (AOWs).
Process Submit ATF Form 4, pay $200 tax stamp ($5 for AOWs), undergo FBI background check, wait 6-12+ months.
The NFA Registry (NFRTR) Formally: National Firearms Registration and Transfer Record. Maintained by ATF NFA Branch, Martinsburg, WV.
Read more →
Nazi Germany: Census and Data Infrastructure Hollerith Tabulating Machines and Dehomag Herman Hollerith invented punch card tabulator for 1890 US Census. IBM (formerly CTR) commercialized globally. Dehomag (Deutsche Hollerith-Maschinen Gesellschaft), IBM’s German subsidiary, customized for German needs — custom-designed cards with columns for religion, nationality, mother tongue.
Edwin Black, IBM and the Holocaust (2001): documents how Dehomag’s technology enabled the Reich to cross-reference census data, identifying Jews and mixed-ancestry individuals. IBM maintained involvement through Geneva office.
Read more →
“We Kill People Based on Metadata” and Related Concepts Michael Hayden Quote Former NSA Director (1999-2005) and CIA Director (2006-2009) General Michael Hayden stated “We kill people based on metadata” at a debate at Johns Hopkins University School of Advanced International Studies (SAIS), April 7, 2014. Debate partner: journalist David Cole.
Context: metadata (call records, geolocation, network analysis) is operationally powerful enough to serve as basis for lethal targeting decisions (drone strikes).
Read more →
Mail Scanning, Package Tracking, and Customs USPS Informed Delivery (launched nationally 2017) USPS photographs exterior of every letter-sized mailpiece processed through automation — approximately 150 billion images per year. Shows sender/recipient names, addresses, postmarks. USPS retains images; provides to law enforcement via mail covers and subpoenas.
Mail Covers (39 CFR 233.3) Postal inspectors authorize recording of all information on outside of mail to/from a target. No warrant or court order required — only postal inspector approval.
Read more →
Loyalty Programs, Retail Purchase Data, and NYC Congestion Pricing Retail Loyalty Programs What They Collect Item-level purchase data: every SKU, timestamp, store location, payment method. Tied to customer profile (name, address, phone, email).
Major Programs Kroger Plus CVS ExtraCare Walgreens myWalgreens (formerly Balance Rewards) Over 90% of US grocery spending linked to loyalty accounts Data Monetization Kroger Precision Marketing (84.51°): monetizes purchase data by selling targeted advertising. CVS and Walgreens similarly leverage for ad targeting.
Read more →
Japanese American Internment via Census Data Executive Order 9066 Signed by President Franklin D. Roosevelt, February 19, 1942. Authorized forced relocation of Japanese Americans from West Coast. ~120,000 Japanese Americans interned, majority US citizens.
Second War Powers Act (March 27, 1942) Suspended confidentiality protections of the Census Act, granting other federal agencies access to individual census records.
Census Bureau Cooperation In 1943, Census Bureau provided War Department with tabulations of Japanese Americans by geographic area.
Read more →
IRS Political Targeting Tea Party / Conservative Group Targeting (2010-2013) The Scandal 2013: Treasury Inspector General for Tax Administration (TIGTA) audit confirmed IRS used inappropriate criteria to identify political organizations applying for tax-exempt status, including selecting groups with “Tea Party,” “Patriots,” or “9/12” in their names for intensive scrutiny.
From 2010-2012, the IRS Exempt Organizations Unit subjected conservative applications to delays and demands for information about political beliefs, plans to run for office, and names of financial backers.
Read more →
Information Theory / Deanonymization Latanya Sweeney (1997) 87% of the U.S. population uniquely identifiable using 5-digit ZIP code, gender, and date of birth.
Golle (2006) found 63% uniquely identifiable from the same three fields using different methodology.
Bits of Information ZIP code: ~23.8 bits Birthday: ~8.5 bits Gender: ~1 bit Total: ~33.3 bits U.S. population (~330M) requires ~28.2 bits (log2 of 330,000,000) to uniquely identify one person ZIP + birthday alone = ~32.
Read more →
Identity Verification KYC (Know Your Customer) Origin: Bank Secrecy Act of 1970. Expanded: USA PATRIOT Act (2001). Data: full legal name, DOB, address, SSN, government-issued photo ID.
Originally banking only; now crypto exchanges, fintech apps, online platforms.
Form 4473 (Firearms Transaction Record) Collects: full legal name, current address, DOB, place of birth, sex, height, weight, race, ethnicity, SSN (optional). Section A/C: firearm make, model, caliber, serial number. Dealer contacts NICS (checks three FBI databases).
Read more →
Identity Verification: Data Breaches and Conflicts of Interest OPM Breach (2014-2015) What Was Exposed 22.1 million records total (revised upward multiple times). Includes 21.5 million SF-86 security clearance forms (finances, mental health, foreign contacts, sexual history, drug use, family members, associates) and 5.6 million fingerprint records. SSNs for all affected. Attributed to Chinese state actors (Jiangsu State Security Department, MSS subsidiary).
Staggered Disclosure March 2014: First breach detected (later revealed to have begun December 2013 via USIS contractor systems) July 9, 2014: NYT publicly revealed intrusion (“Chinese Hackers Pursue Key Data on U.
Read more →
Google and Intelligence Community Funding MDDS (Massive Digital Data Systems) Program Launched 1993 by the US intelligence community. Sponsors: NSA, CIA Office of Research & Development, intelligence community’s Community Management Staff (CMS). Funding: ~$3-4 million/year for 3-4 years. Managed for CIA and NSA by military and intelligence contractors. Program was unclassified but highly compartmentalized.
The Stanford Grant 1995: one of the first MDDS grants went to a computer science research team at Stanford University with a decade-long history of NSF and DARPA grants.
Read more →
Facial Recognition: Airports and DMVs Airport Facial Recognition TSA CAT-2 Units TSA Credential Authentication Technology with facial matching. Deployed to 80+ airports as of early 2024 (including ATL, DTW, LAX, DCA). TSA states participation optional for US citizens; travelers may request manual document review. Advocacy groups (ACLU, EFF) report opt-out poorly communicated and practically difficult.
CBP Biometric Entry-Exit Mandated by Congress (2004 Intelligence Reform Act, reinforced 2016). Facial comparison at departure gates.
Read more →
Encryption, “Going Dark,” and EO 12333 FBI vs. Apple (San Bernardino, 2016) December 2, 2015: Syed Rizwan Farook and Tashfeen Malik killed 14 in San Bernardino. FBI recovered Farook’s county-issued iPhone 5C (iOS 9).
February 16, 2016: Magistrate Judge Sheri Pym (C.D. Cal.) issued order under All Writs Act (28 U.S.C. 1651) compelling Apple to build custom firmware (“GovtOS”) to disable auto-erase and brute-force delay. In re Search of an Apple iPhone, Case No.
Read more →
Employer Surveillance (Bossware) and School Surveillance Employer Surveillance Growth During COVID Gartner (April 2022): 60% of large employers deployed monitoring software, up from ~30% pre-pandemic Digital.com (2022): 60% of companies with remote workers used monitoring ExpressVPN (2021): 78% of employers used at least one monitoring tool American Management Association (2023): 80%+ of major companies engaged in electronic monitoring What These Tools Do Keystroke logging, periodic/triggered screenshot capture, webcam activation, application/website tracking, productivity scoring, idle-time detection, email and messaging monitoring.
Read more →
Drones: FAA, FCC, and Purchasing Restrictions FAA Remote ID Final Rule: 14 CFR Part 89, published January 15, 2021 Compliance deadline: September 16, 2023 All drones requiring registration must broadcast Remote ID Broadcast Data Drone serial number or session ID, drone lat/long/altitude, operator lat/long/ altitude, takeoff location, timestamp, emergency status. Broadcast via Bluetooth 4/5 or Wi-Fi NaN. Receivable by anyone within range (~300m-1km) with compatible device or app (DroneScout, OpenDroneID).
Read more →
DNA and Genetic Privacy 23andMe Data Breach (2023) Began April 2023. Credential stuffing attack: usernames/passwords from other breached sites fed into 23andMe login. Ran ~5 months before detection. Affected ~7 million customers (6.4 million US-based).
Data exposed: raw genotype data, health predisposition reports, carrier-status reports. Via DNA Relatives feature: profile information of ~5.5 million additional users plus Family Tree information of 1.4 million individuals.
UK ICO and Canada OPC found 23andMe failed to implement appropriate security (no mandatory MFA, inadequate password requirements).
Read more →
Data Management Platforms (DMPs) What They Are Centralized systems that collect, organize, and activate first-, second-, and third-party audience data from websites, mobile apps, CRM systems, and ad campaigns. Build user profiles and segment them for targeted advertising.
How They Work Collection: Data from webpage visits, registration forms, mobile devices, social networks, smart devices, offline purchases Organization: Data analyzed and categorized into taxonomies to build user profiles Activation: Segments pushed to DSPs, SSPs, CDPs, CRM systems via APIs Major DMP Providers Oracle Data Cloud (BlueKai) Lotame Adobe Audience Manager Data Characteristics Profiles are pseudonymous (tied to device IDs, cookie IDs, or advertising IDs) DMPs merge first-party data (what user told the website) with third-party data (data broker information) When a DMP syncs IDs with a DSP, pseudonymous IDs can be linked across systems Sources https://www.
Read more →
Digital License Plates, V2X, and Private ALPR Digital License Plates (Reviver) What They Are Reviver is sole company with FCC-approved digital plates (“RPlate”). E-ink display with built-in GPS and cellular connectivity. Can be remotely updated to display “STOLEN,” show custom messages (parked mode), auto-renew registration.
Legal In California, Arizona, Michigan, Texas (as of early 2025). Additional states considering.
Data Collection System logs vehicle location, timestamps, can track speed. Plate communicates with Reviver’s cloud platform.
Read more →
Deplatforming: Specific Cases GoDaddy / Arfcom Arfcom (AR15.com), one of the most popular gun forums on the internet, had hosting pulled by GoDaddy (Amazon partner) without warning or explanation.
Google / Blogger “No Lawyers, Only Guns and Money” (veteran rights and gun blog) removed from Blogger (Google) for “promoting or selling regulated items.” Later restored; Google cited automated system.
Google, Facebook, Instagram — Advertising Bans Google Ads prohibits promotion of firearms, ammunition, explosives, gun parts, and related accessories.
Read more →
Deceptive Framing: “It’s Not a Database” A recurring pattern across government and corporate surveillance infrastructure: systems are described in technically narrow terms that most people would consider misleading.
REAL ID: “Does Not Create a National Database” The Claim DHS FAQ: REAL ID “does not create a national database.” Source: https://www.tsa.gov/realid/realid-faqs
The Reality REAL ID requires every state DMV to be queryable from a centralized clearinghouse. The system is called S2S (State to State Verification Services) and relies on a central database called SPEXS (State Pointer Exchange Services).
Read more →
Debanking: Operation Choke Point and SARs Operation Choke Point (2013-2017) DOJ and FDIC initiative targeting legal but disfavored industries through banking relationships.
Mechanism: Banks received “guidance” that serving certain industries created “reputational risk.” DOJ invoked FIRREA’s “self-affecting” theory — banks harmed themselves by serving disfavored industries. No law passed, no regulation issued.
FDIC 30-item “high risk” list included:
Gun and ammunition sales Payday lenders Debt collectors Money services businesses Pornography Fireworks sellers Impact: One major lender turned away by 275 banks.
Read more →
Death of Cash and Financial Weaponization Cash Decline US: cash accounted for 20% of transactions in 2023 (Federal Reserve Diary of Consumer Payment Choice), down from 31% in 2016 UK: cash payments fell from 63% (2006) to 14% (2022) (UK Finance) Sweden: cash under 10% of transactions; Riksbank piloting e-krona India: PM Modi demonetized 500/1000-rupee notes November 8, 2016, invalidating ~86% of currency in circulation overnight IRS $600 Reporting Threshold Section 9674 of American Rescue Plan Act (2021) lowered 1099-K reporting threshold from $20,000/200 transactions to $600.
Read more →
Data Brokers and Government Access Fog Data Science Sold Fog Reveal tool to law enforcement. AP investigation (September 2022): ~80 agencies purchased or tested it, including local police and Arkansas State Police. Contracts $6,000-$9,000/year. EFF obtained FOIA records showing granular device tracking at specific locations. Data sourced from smartphone ad ecosystem.
Venntel (Gravy Analytics subsidiary) CBP and ICE purchased location data. CBP paid ~$476,000 (2018-2020, USAspending). DHS Inspector General report (September 2023): CBP, ICE, Secret Service used commercial telemetry data without adequate privacy safeguards.
Read more →
Credit Reporting The Big Three Equifax, Experian, TransUnion maintain credit files on virtually every American adult.
Data Collected Payment history on all credit accounts (cards, mortgages, auto, student loans) Outstanding debts and credit utilization Account opening/closing dates Public records: bankruptcies, liens, judgments, court filings Collections accounts Hard and soft inquiries Employment history (Equifax Workforce Solutions) Historical addresses Demographic data Specialty Bureaus (CFPB lists dozens) LexisNexis Risk Solutions: Real estate transactions, property ownership, lien/judgment/bankruptcy records, professional licenses, criminal history, insurance claims (auto, homeowners — amounts, dates, circumstances), historical addresses, phone records, utility records, license plates, employment history, known associates.
Read more →
COVID-Era Privacy Erosion Contact Tracing Promises Broken Singapore (January 2021): Police accessed TraceTogether contact tracing data for criminal investigations despite explicit public health-only promises. Parliament subsequently passed legislation restricting (not eliminating) police access.
Australia (June 2021): Western Australia police sought access to SafeWA check-in app data for criminal investigations.
South Korea: Quarantine location data used in criminal investigations. Leaked data enabled doxxing. Corona 100m app published location histories of infected individuals (age, gender, locations visited).
Read more →
Connected Cars and IoT Surveillance Connected Cars GM / LexisNexis (March 2024) NYT (Kashmir Hill): GM collected driving data (speed, braking, acceleration) through OnStar Smart Driver program, sold to LexisNexis Risk Solutions and Verisk Analytics. Brokers generated “risk scores” sold to insurance companies to raise premiums. Many drivers enrolled without clear understanding of consent. GM ended Smart Driver data-sharing following reporting.
What Modern Cars Collect 100+ sensors per vehicle, always-on cellular modems.
Read more →
Commercial Facial Recognition: Retail, False Accusations, Clearview AI Retail Facial Recognition Rite Aid — FTC Action (December 2023) Deployed facial recognition in hundreds of stores, disproportionately in predominantly Black and Asian communities. FTC banned Rite Aid from using facial recognition for five years. Findings: system generated false-positive matches leading to employees wrongly accusing, following, or calling police on customers. Rite Aid failed to test for racial or gender bias and ignored known inaccuracies.
Read more →
Cell Phone Carriers: Data Collection and Sharing Data Collected by Major US Carriers (Verizon, AT&T, T-Mobile) Call detail records (CDRs): numbers dialed, duration, timestamps Cell site location information (CSLI) from tower connections SMS metadata Mobile browsing history (via DNS queries; historically deep packet inspection) App usage data Device identifiers (IMEI, IMSI) CDRs triangulate location to ~50-300 meters in urban areas. Retention: 1-2 years (AT&T reportedly up to 7 years for call records).
Read more →
Car Telematics in Divorce, Custody, and Domestic Abuse Cases Tesla Remote Control as Abuse Tool Reuters “Deadly Connections” investigation (December 2023): documented multiple cases where domestic-abuse survivors reported estranged partners used Tesla’s app to remotely track vehicle location in real time, remotely lock/unlock doors, manipulate climate controls, flash headlights — all without physical access to the car. Victims unable to remove spouse’s app access because Tesla ties control to account holder, not driver.
Read more →
Boston Marathon Bombing: Shelter-in-Place and Warrantless Searches (2013) Reference thread: https://www.ar15.com/forums/general/Continued-The-Boston-bombing-and-how-martial-law-was-enacted/5-2841380/ (Arfcom thread documenting events; fetched 403 — review manually for firsthand accounts and photos)
Timeline April 15, 2013: Boston Marathon bombing (Tsarnaev brothers). 3 killed, 264 injured. April 18-19, 2013: MIT officer killed. Shootout in Watertown, MA. Tamerlan Tsarnaev killed. Dzhokhar Tsarnaev fled on foot. The Lockdown Governor Deval Patrick ordered nearly one million people to “shelter in place.” Businesses, schools, courthouses shut down.
Read more →
Bluetooth, WiFi, and Retail Location Tracking WiFi Probe Request Tracking Phones broadcast WiFi probe requests containing MAC addresses when scanning for networks. Retailers exploited this for foot traffic analytics.
Key Companies Euclid Analytics (founded 2010, acquired by WeWork 2019) RetailNext (founded 2007) Placed (acquired by Snap Inc. 2017) InMarket (founded 2010, merged with NinthDecimal 2021) Data Collected Device MAC addresses, dwell time per zone, walking path through store, repeat visit frequency, cross-store movement patterns.
Read more →
ATF / NICS / Gun Records Legal Prohibition on Registry FOPA (1986), 18 U.S.C. 926(a): “No system of registration of firearms, firearms owners, or firearms transactions or dispositions may be established.”
Appropriations riders (FY1979-FY2012, made permanent with “hereafter”): block ATF from requiring FFLs to submit sales reports.
NICS destruction mandate (FY2004-FY2012, made permanent): FBI must destroy approved background check records within 24 hours.
What ATF Holds 920,664,765 firearm records as of late 2021.
Read more →
ATF Misconduct Operation Fast and Furious (2009-2011) ATF Phoenix Field Division allowed ~2,000 firearms to “walk” to Mexican cartel operatives. Border Patrol Agent Brian Terry killed December 14, 2010; Fast and Furious weapons at scene. DOJ OIG report (September 2012): 14 officials found responsible. AG Eric Holder held in contempt of Congress June 28, 2012.
Forced Reset Trigger Reclassification (2022-2023) ATF reclassified Rare Breed FRT-15 triggers as “machine guns” after legal sale.
Read more →
Apple & Google: Vertical Integration in Mobile Google Alphabet 2023 ad revenue: $237.86 billion (10-K filing).
Data collection via Android: GPS location, WiFi scanning, app usage, sensor data. Chrome: 65%+ global browser share (StatCounter). Gmail: 1.8B users. Google Pay tracks purchases.
Google controls: demand side (Google Ads, DV360), supply side (AdSense, Ad Manager), exchange (AdX), measurement (GA4), DNS (8.8.8.8), CDN (Google Global Cache).
Location History Scandal (2018) AP investigation (August 13, 2018): Google tracked location data even when “Location History” was explicitly turned off, via separate “Web & App Activity” setting.
Read more →
Anthrax Vaccine (AVA/BioThrax) Malfeasance AVIP Mandate Anthrax Vaccine Immunization Program announced by SecDef William Cohen, December 1997. Vaccinations began March 1998. Goal: vaccinate all 2.4 million active-duty and reserve personnel. By 2000: ~500,000 had received at least one dose. Partially suspended 2000 (supply shortages), restarted in limited form 2002 after anthrax letter attacks.
BioPort / Emergent BioSolutions Michigan Biologic Products Institute (state-owned) was sole AVA manufacturer. 1998: BioPort Corporation formed, acquired facility for ~$25 million.
Read more →
AI Chat History as Discoverable Evidence Courts treat AI prompts and outputs as electronically stored information (ESI), subject to same discovery rules as emails and text messages.
OpenAI v. New York Times (2025-2026) January 2026: Judge Sidney Stein upheld order requiring OpenAI to produce 20 million ChatGPT conversation logs in NYT copyright litigation. Users whose conversations were included received no notification, no opportunity to object. May 13, 2025: Magistrate Judge Ona Wang ordered OpenAI to “preserve and segregate all output log data that would otherwise be deleted on a going-forward basis” — including chats users had explicitly deleted or that privacy laws would otherwise require erasure.
Read more →
